My Opinion on Digital Forensic Steps when I was a Young Student
Note
This is the fifteenth assignment from my Masters Advanced Network Security Course which has never been published anywhere and I, as the author and copyright holder, license this assignment customized CC-BY-SA where anyone can share, copy, republish, and sell on condition to state my name as the author and notify that the original and open version available here.
1. What is Digital Forensic?
Digital forensic is a part of forensic science that recovers and investigates materials found in digital devices. Digital forensic can be computer forensic, network forensic, forensic data analysis, mobile device forensic, and anything that includes digital data. Digital forensics is widely known in gaining evidence from digital data to support justification of a crime incident, like finding the information exchange between suspects using digital media (some call it E-discovery). Very similar to digital crime investigation (DCI) which distinguish digital forensic itself as a process of digging evidence from digital device, while DCI itself is the use of digital device to help gain evidence of a crime incident. Other than supporting crime investigation digital forensic is often known to investigate certain events on the digital world. [1]
2. Why Need The Digital Forensic?
Digital technologies are becoming part of our lives, or maybe already are. Everyday we are using digital devices, and making Hollywood movies came to reality where information about certain individuals, their signatures, even evidence can be found in digital devices. More than 100 years ago we didn’t treat blood, finger prints, and food prints as important evidence since science back cannot extract information of an event. Today is different where blood and finger prints can show the individual responsible on that scene. Recently digital evidence is making the same trend. With investigation on the digital device we can tell who the users are, where they are, what for and when they used it. [2]
On the first section states of real world incidents, but it’s not only there that incidents occur, but also on the digital world. The term cyber threat is known now like theft of private information, online fraud, and damages due to malwares occurs. On the real world incidents we intent find who the culprit to press charges on the court but on the digital world the question “who” is not as important as “how”. We can find who breached the information security and who created the malware to press charge against them, but if that’s the only thing then we can expect even more attacks in the future. How the breached occurs and how the malware works is the important thing to make a defense mechanism for future attacks. Through digital forensic we obtain these information to apply security based on the threat. [3]
3. How to Perform Digital Forensic?
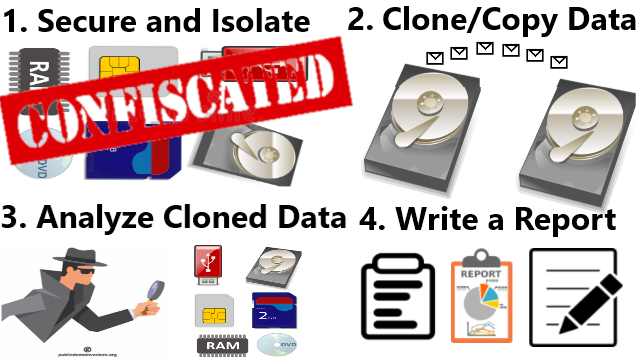
Generally there 4 steps [4]:
- Seizure: the process of obtaining the devices to to be analyze.
- Acquisition: the process of duplicating the information contain on a digital device. In Linux an application called “disk-disk” (dd) can be used, and not forget to use hashing like MD5 to confirm the integrity of data (make sure the data was not tampered). [5]
- Analysis: this is the main process to find evidence and a very specialist field. The original data must not be touched instead we use the duplicated data from the previous process. Examples are examining the logs, metadata, capture packets with Wireshark, files, directories, etc. The process of log analysis alone is already very wide. [6]
- Reporting: the final and deterministic step with no matter how skilled we are in gathering digital evidence, it’s no use if we cannot make a decent report or present the results well. Tools like Encase and Forensic Tool Kit (FTK) can generate nice reports. [7]
4. Reference
- https://en.wikipedia.org/wiki/Digital_forensics
- http://ellwoodevidence.com/digital-forensics-why
- http://www.darkreading.com/attacks-breaches/why-digital-forensics-in-incident-response-matters-more-now/a/d-id/1318254
- https://en.wikipedia.org/wiki/Digital_forensic_process
- http://null-byte.wonderhowto.com/how-to/hack-like-pro-digital-forensics-using-kali-part-2-acquiring-hard-drive-image-for-analysis-0155533
- http://md.kumamoto-u.ac.jp/course/view.php?id=38348
- http://null-byte.wonderhowto.com/how-to/hack-like-pro-digital-forensics-using-kali-part-1-the-tools-forensic-investigator-0155427
Mirrors
- https://www.publish0x.com/fajar-purnama-academics/my-opinion-on-digital-forensic-steps-when-i-was-a-young-stud-xpnldzq?a=4oeEw0Yb0B&tid=github
- https://0darkking0.blogspot.com/2021/02/my-opinion-on-digital-forensic-steps.html
- https://0fajarpurnama0.medium.com/my-opinion-on-digital-forensic-steps-when-i-was-a-young-student-9659afd07c3f
- https://0fajarpurnama0.github.io/masters/2020/07/21/opinion-digital-forensic-steps
- https://hicc.cs.kumamoto-u.ac.jp/~fajar/masters/opinion-digital-forensic-steps
- https://steemit.com/technology/@fajar.purnama/my-opinion-on-digital-forensic-steps-when-i-was-a-young-student?r=fajar.purnama
- https://stemgeeks.net/technology/@fajar.purnama/my-opinion-on-digital-forensic-steps-when-i-was-a-young-student?ref=fajar.purnama
- https://blurtter.com/blurtech/@fajar.purnama/my-opinion-on-digital-forensic-steps-when-i-was-a-young-student?referral=fajar.purnama
- https://0fajarpurnama0.wixsite.com/0fajarpurnama0/post/my-opinion-on-digital-forensic-steps-when-i-was-a-young-student
- http://0fajarpurnama0.weebly.com/blog/my-opinion-of-xsscss-digital-forensic-and-digital-crime-investigation-when-i-was-a-young-student
- https://0fajarpurnama0.cloudaccess.host/index.php/9-fajar-purnama-academics/206-my-opinion-on-digital-forensic-steps-when-i-was-a-young-student
- https://read.cash/@FajarPurnama/my-opinion-on-digital-forensic-steps-when-i-was-a-young-student-2ac8c7e9
- https://www.uptrennd.com/post-detail/my-opinion-on-digital-forensic-steps-when-i-was-a-young-student~ODYyNzU1