Penetration Testing
Denial of Service (DOS) on Wifi using Ostinato Linux
There was no CommView in Linux where I used it to perform DoS. However, I found a similar software called Ostinato and it can work for Dos.
Keywords: Linux DoS denial of service wifi Ostinato
Denial of Service (DOS) Pada Wifi Menggunakan Ostinato Linux
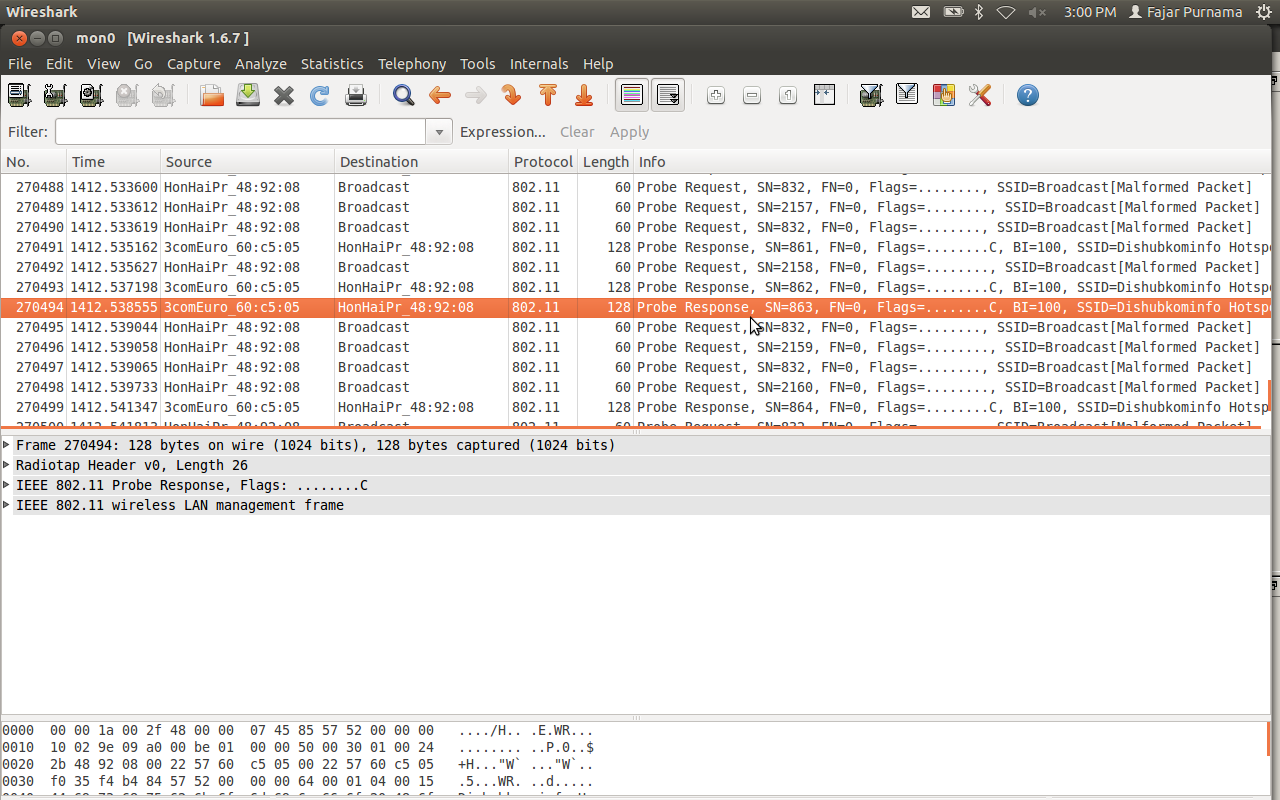
Tidak ada CommView di Linux untuk melakukan DoS. Namun, saya menemukan perangkat lunak serupa yang disebut Ostinato dan dapat Dos.
Keywords: Linux DoS denial of service wifi Ostinato
Denial of Service (DOS) on Wifi using CommView Windows
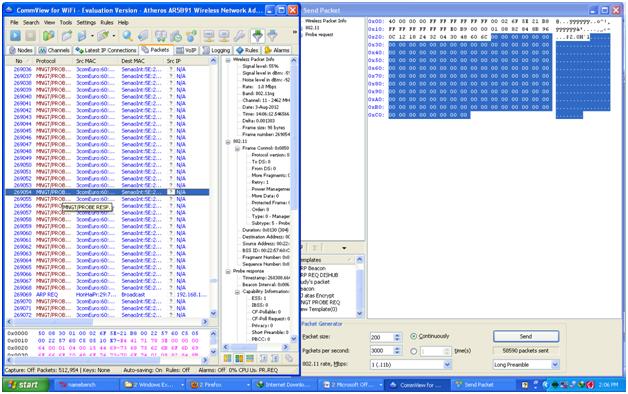
DOS prevents other users from doing activities on the network. Here I will demonstrate DOS on a wifi using CommView for WiFi on Windows.
Keywords: Windows DOS denial of service wifi CommView
Denial of Service (DOS) Pada Wifi Menggunakan CommView Windows
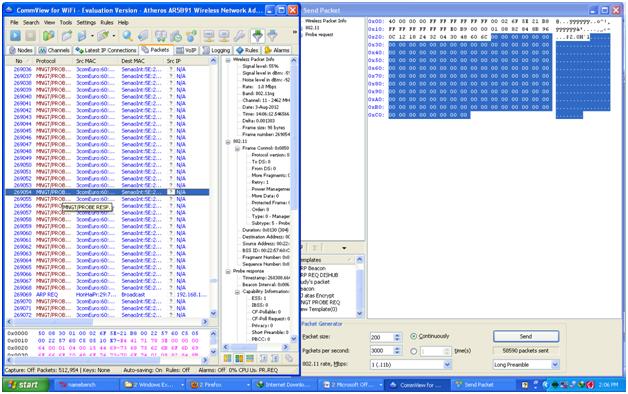
DOS mencegah pengguna lain beraktivitas di jaringan. Di sini saya akan mendemonstrasikan DOS pada wifi menggunakan CommView for WiFi di Windows.
Keywords: Windows DOS denial of service wifi CommView
Simple Password Bruteforce Demonstration Using Hydra

I can define password brute forcing in just one sentence which is trying every single character combination to crack a password.
Keywords: penetration testing brute force Hydra Linux Backtrack NMAP
Demonstrasi Bruteforce Sederhana Menggunakan Hydra

Saya dapat mendefinisikan password bruteforce hanya dalam satu kalimat yaitu mencoba setiap kombinasi karakter untuk memecahkan kata sandi.
Keywords: penetration testing brute force Hydra Linux Backtrack NMAP
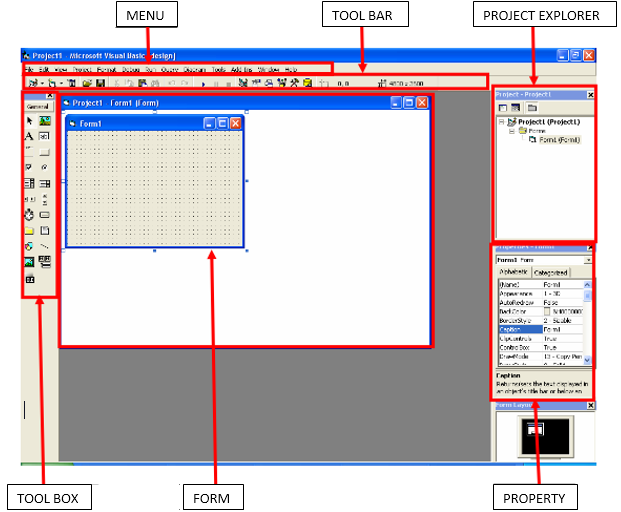
Having a Taste of Being a Hacker
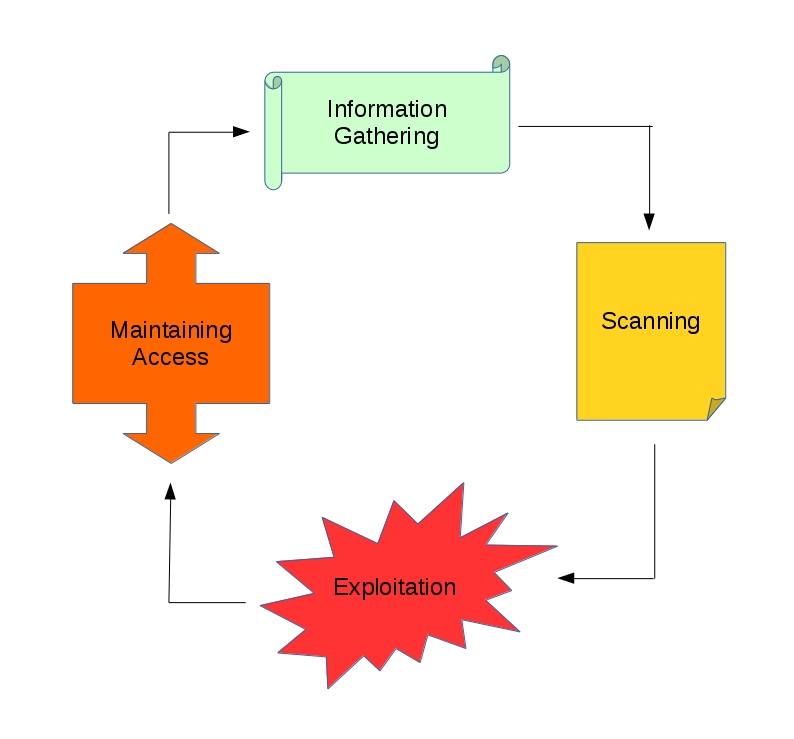
There are four main steps in penetration testing which are (1) Information Gathering, (2) Scanning, (3) Exploitation, (4) Maintaining Access
Keywords: penetration testing hacking information gathering scanning exploitation maintaining access metasploit nmap theharvester openvas ping nslookup Google white hat grey hat black hat
Cicipan Menjadi Hacker
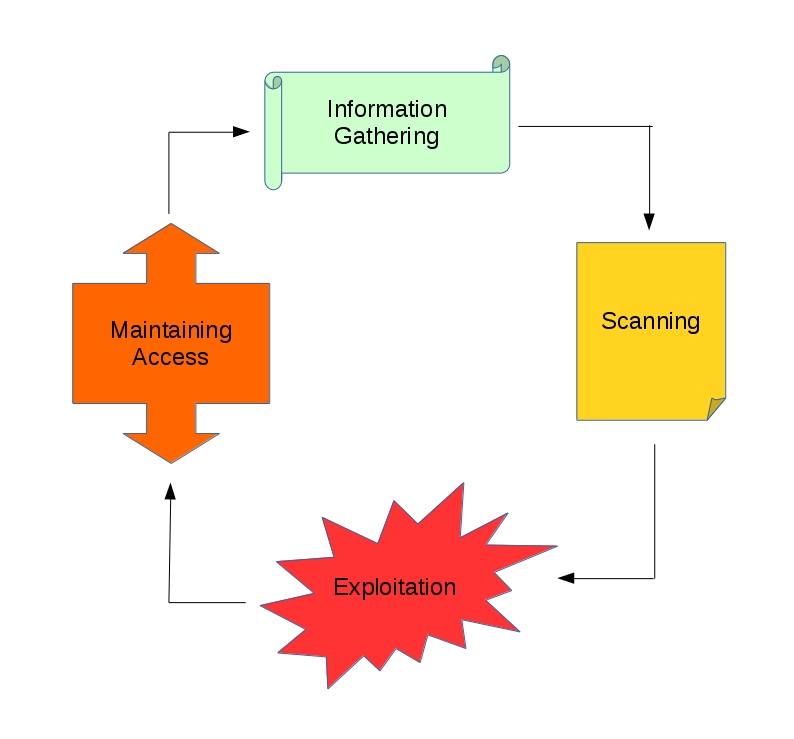
Ada empat langkah utama dalam pengujian penetrasi (1) Pengumpulan Informasi, (2) Pemindaian, (3) Eksploitasi, (4) Mempertahankan Akses.
Keywords: hacker pentest pengumpulan informasi pemindaian eksploitasi pemeliharaan akses metasploit nmap theharvester openvas ping nslookup Google white hat grey hat black hat
Hacking Sethc and Office Trend USB Windows 7 When You Have Physical Access

The method uses physical means through a bootable media to gain access to administrative command line (cmd.exe here) and exploit sethc.exe.
Keywords: Bypass Blocks USB Access Micro Trend Hacking Administrative Access Windows 7 sethc vulnerability